Hello,
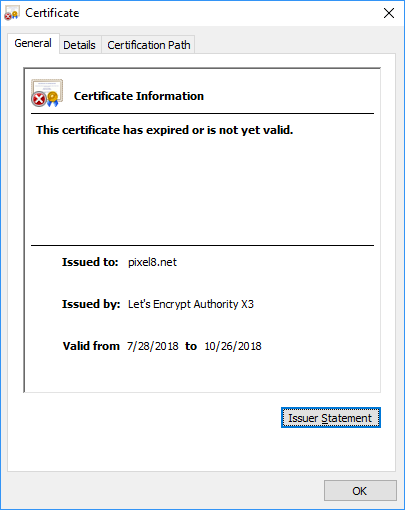
I’m new to the certs thing. I’m running a Windows Server 2016 OS. Using Certify the Web client I added certs to my domain pixel8.net. It all worked fine. Now that the time frame is up on the original cert, it shows as being expired
The cert date in the Certify the Web client is different, and it shows as not being expired (It’s renewed multiple times since the original installation).
I checked the bindings in IIS and it looks like it’s using the latest cert dates I’m not sure what I’m missing. Any help would be greatly appreciated.
Thanks,
Mike
Hi Mike, sorry to hear it’s not working. There was a bug in v4.0.9 where some bindings didn’t get updated with the latest cert so if you’re on that version you should upgrade immediately. If you’re on v4.0.10 already, open the app and go to the managed certificate for pixel8.net, then click Show Advanced Options and go to Other Options. There you get an option to ‘Re-apply certificate to bindings’. Try that and see if it fixes it.
If that doesn’t work, check the binding is scheduled to be updated in the ‘Preview’ tab, it should say it’s going to update the binding when it next renews, if it doesn’t say that then you’d need to check which options are selected in the Deployment tab.
Thanks for your response. I am on version 4.0.10. I tried “Re-apply certificate to bindings” and the cert still shows expired in the web browser.
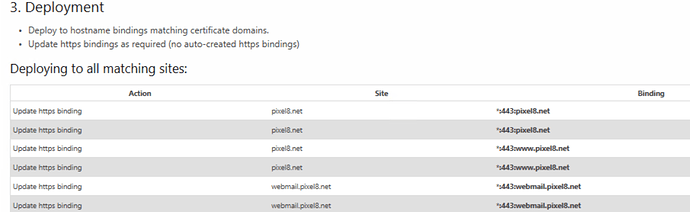
I’m a little confused on the second part. I looked in the preview tab and see the following:
It looks like it has double entries. Is this correct?
Thanks,
Mike
@mgraveen thanks, yes showing double entries is definitely not normal at all. If you look in the IIS binding for the site I assume only one https binding shows? I also see that it’s planning to update webmail.pixel8.net which it should only be doing if you are using a wildcard cert (are you?) or if your cert contains all of: pixel8.net, www.pixel8.net and webmail.pixel8.net
In the bindings I see (2) bindings for port 443 on pixel8.net. 1 with the IP address and 1 with an *. The same with www.pixel8.net. Should they both be there? I’m not sure if I’m using a wildcard. Is there a way to tell?
Thanks,
Mike
Hi Mike,
Sorry I forgot to reply to this. Remove the https binding against the IP unless you are trying to support old clients like Windows XP (in which case remove the old https binding).
So each full hostname should have 1 http binding (optionally) and 1 https binding (only).
The IP specific binding will actually take precedence over any request to the server for any website if it ends up coming in on that IP address (which it probably does), so then you run into the possibility of serving the wrong certificate.
In general, IP specific bindings are a recipe for pain on Windows unless you have a distinct requirement for them. A specific IP per certificate used to be required on Server 2008 and lower but then they introduced SNI (server name indication) which takes the hostname of the site your trying to access and presents the correct certificate (if the https binding for the site has SNI switched on, and has no specific IP).
My recommendation: ensure you only have one https binding in IIS per hostname (e.g. pixel8.net) and ensure it is has IP set to (All Unassigned) or *, and SNI is enabled. Then check your site using an ssl checker like this one: https://www.ssllabs.com/ssltest
Also unless you need it to be otherwise, set Deployment to Auto in Certify and check the Preview to ensure it’s going to update one https binding per domain. You can try the re-apply certificate option to ensure it’s working ok.