Hello,
Per Production Chain Changes - API Announcements - Let's Encrypt Community Support , Let’s Encrypt was to move to the “Long Chain” as of May 4th, however as of today, I am still getting this chain: End-entity certificate ← R3 ← DST Root CA X3
I have configured the Preferred Chain option to be “ISRG Root X1”, which is the actual chain I need ( End-entity certificate ← R3 ← ISRG Root X1) , yet Certify App still is pulling down the cert and old chain (End-entity certificate ← R3 ← DST Root CA X3).
Is there something I need to look for / configure / re-do to get the chain that I need. I have pinged a colleague of mine who has a similar CertifyTheWeb app setup and they are getting the chain I do want, with a default certify the web app config … ( End-entity certificate ← R3 ← ISRG Root X1) --makes no sense unless Let’s Encrypt has not fully rolled things out…
Thoughts?
TIA
S
All of my certificates from Certify and acme.sh still use the chain that will expire at the end of September. But with the certificates expiring before September, I don’t really see it as an issue. I’ll have to renew all of them before the CAs expire anyways.
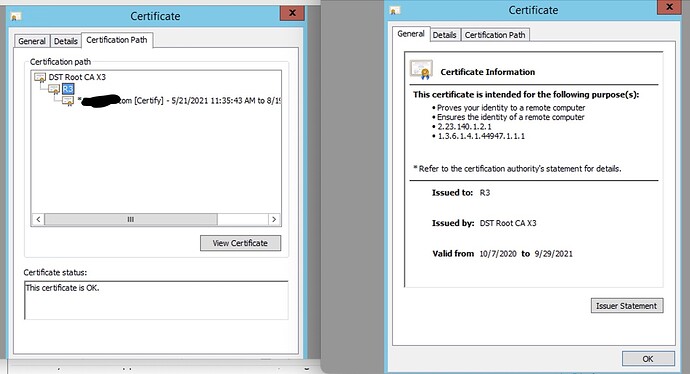
The question is how are you verifying your certificate chain, R3 is cross signed so either ISRG Root X1 or DST Root CA X3 can vouch for it. If you use the built in windows certificate viewer it uses which ever path it likes the most (so R3 usually looks like it’s root is DST Root CA X3).
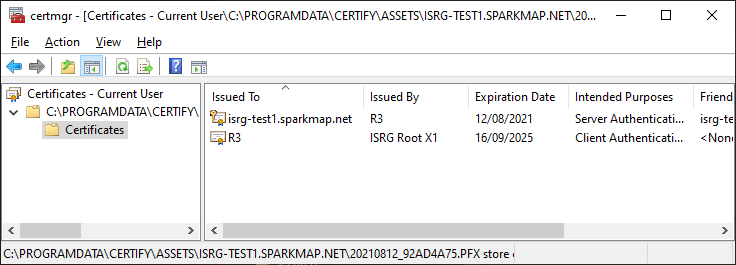
If you open the certificate with the view that shows you the individual components (for me that’s right click the PFX and choose Open) you can see the ISRG Root X1
Cert Chain listed below. Still have the old ‘short’ chain. I’ve tried specifying the alternate chain (ISRG Root X1) within the application and it does not work, still get the soon to be expired short chain…
They’ve talked about cross-signing for a while… and frankly, I don’t understand it fully.
But more to the point, I don’t understand your issue. You have a certificate that expires on Aug 15th. Why do you care that the intermediary expires at the end of September? You won’t even have that certificate anymore because you’ve probably renewed 1-3 times between now and then.
Lastly, I read this written somewhere… clients build the path they want, not the one you want. So if you have two valid certificate chains, the client is going to show you one. Just one. Which ever one it felt like.
Your example is using the build in windows certificate viewer, which as stated, just builds whatever path it wants. Try certutil -dump your_certificate.pfx (enter key for blank password). Here’s the example output I get. Note the first cert is R3 intermediate with the ISRG Root X1 issuer.
================ Certificate 0 ================
================ Begin Nesting Level 1 ================
Element 0:
Serial Number: 912b084acf0c18a753f6d62e25a75f5a
Issuer: CN=ISRG Root X1, O=Internet Security Research Group, C=US
NotBefore: 4/09/2020 8:00 AM
NotAfter: 16/09/2025 12:00 AM
Subject: CN=R3, O=Let's Encrypt, C=US
Non-root Certificate
Cert Hash(sha1): a053375bfe84e8b748782c7cee15827a6af5a405
---------------- End Nesting Level 1 ----------------
No key provider information
Cannot find the certificate and private key for decryption.
================ Certificate 1 ================
================ Begin Nesting Level 1 ================
Element 1:
Serial Number: 03a142d0d38054c1aa773db0dfd8b950f73f
Issuer: CN=R3, O=Let's Encrypt, C=US
NotBefore: 14/05/2021 11:48 AM
NotAfter: 12/08/2021 11:48 AM
Subject: CN=isrg-test1.sparkmap.net
Non-root Certificate
Cert Hash(sha1): 33553d536aa98af5f2d6180d6110b2f1604a7b89
---------------- End Nesting Level 1 ----------------
Provider = Microsoft Enhanced Cryptographic Provider v1.0
Certificate Public Key:
Version: 3
Public Key Algorithm:
Algorithm ObjectId: 1.2.840.113549.1.1.1 RSA
Algorithm Parameters:
05 00
Public Key Length: 2048 bits
Public Key: UnusedBits = 0
0000 30 82 01 0a 02 82 01 01 00 9f f6 2a b5 90 42 d9
0010 6a 06 05 71 b9 22 e4 55 75 96 0c 67 d4 04 77 50
0020 49 e8 68 e1 8d 4f 92 27 2c 02 01 a8 95 d4 47 46
0030 7e b5 91 76 af 85 41 41 7a 3b 87 ba d0 2b fb 59
0040 69 ee 9e 6c 8d 63 f6 16 8c 88 13 5b 56 f5 54 ac
0050 00 44 40 59 5b d6 18 0d 8e a8 e6 1e a5 ca e8 3b
0060 a6 2e 05 16 a9 9c bb 25 3c 06 f4 54 28 8f 06 ed
0070 1b 9f f9 81 14 c8 11 95 04 b0 36 4e fb ed 41 da
0080 77 f9 14 38 ce 82 81 ab 5f 93 53 2e f4 07 7a dc
0090 e7 be cd 06 3f 82 a3 4c f9 ba 44 40 15 77 b4 51
00a0 98 64 a1 65 a0 5f 1b ce ab 86 4f 17 ff eb 79 f8
00b0 1f 20 4d 45 b9 5a e2 db 14 07 79 c2 84 1f 4d a5
00c0 3a a3 cf 83 b6 ef eb 4b 66 7a d0 46 43 95 14 a3
00d0 2a 7e c8 13 d3 6e dc f8 5f 1b 99 4e 15 96 93 dd
00e0 eb 0e d4 d6 b0 7f 06 22 19 4b 4c e9 93 ec 97 53
00f0 a0 e4 4b 86 e5 12 f4 94 ec 26 5d 1d 4f 7a b6 ff
0100 cf 6b fc 56 a0 4a c7 00 91 02 03 01 00 01
Key Id Hash(rfc-sha1): 0c7dcc57faaeff2c2fe28739d91abf58cf195961
Key Id Hash(sha1): 393d49a77e8c3b4ee03a87c45e1cd938c52e4905
Key Id Hash(bcrypt-sha1): 84ac374cf0f499493ea5e3ddf1eb4201cd44189a
Key Id Hash(bcrypt-sha256): 5c2d4a571f4f501e4bde625dc40ef93c77f24fb59aa54b89a5782ebda2a722d7
Container Public Key:
Public Key Algorithm:
Algorithm ObjectId: 1.2.840.113549.1.1.1 RSA
Algorithm Parameters: NULL
Public Key Length: 2048 bits
Public Key: UnusedBits = 0
0000 30 82 01 0a 02 82 01 01 00 88 8c c1 9a df c2 8b
0010 74 b1 49 87 e7 19 3d 43 12 2e 94 9b 2c 35 96 b0
0020 02 fa f7 b6 b9 fc f3 a6 ed f5 8c 36 1a a1 1b b4
0030 24 b6 ed 69 91 12 b6 98 a1 c5 b0 39 1d c8 27 39
0040 23 36 29 67 cd 63 54 01 40 ef c5 66 48 07 8f 0e
0050 89 b5 8e 93 12 1a 73 9f 8e 10 aa 0e 8e 7c 16 8a
0060 79 c5 2c 3f 11 f8 f4 58 df 12 01 c6 12 89 7e 98
0070 11 2c e4 95 15 19 37 d4 a5 e9 1c 08 9f 35 a3 0c
0080 00 2d e9 89 77 a4 de aa d2 9b 4c 67 a0 82 ec 06
0090 2f 48 ec c1 48 df f2 fa 3d fa 89 2c cd b3 c4 e3
00a0 f1 58 af 78 83 a5 43 a5 f2 de c7 72 cc a9 f0 47
00b0 e5 17 a2 df e1 81 d3 57 23 ad 8a 28 29 7c 26 12
00c0 16 ea 9d 50 33 e0 ce 76 72 20 a9 51 e6 ab 46 14
00d0 01 bd 55 ad 83 0f db e0 a5 8c 16 04 c0 07 12 8b
00e0 2d b3 1e 7d 5f 17 ad 78 82 3b 01 01 29 9f 6d 11
00f0 23 3d fa 49 74 28 3a 3d 58 93 e9 61 d1 de 72 68
0100 12 2b 4f fa 7d 6a 71 23 cf 02 03 01 00 01
Key Id Hash(rfc-sha1): b67c78650d371183981b0302a5f0d941d7dbf0c8
Key Id Hash(sha1): 328b76d4458dee1792130205e927ee94f5affdc3
Key Id Hash(bcrypt-sha1): 1daeb878bacd328a33c925e5cb52c6a656b077f8
Key Id Hash(bcrypt-sha256): 8e5f9910007b752da3429d0c23f163539255f6b59bc4342ae7084df900510cb8