Hi,
I recently wanted to update my certificates but I ran into problems using the newest version 5.6.8.0.
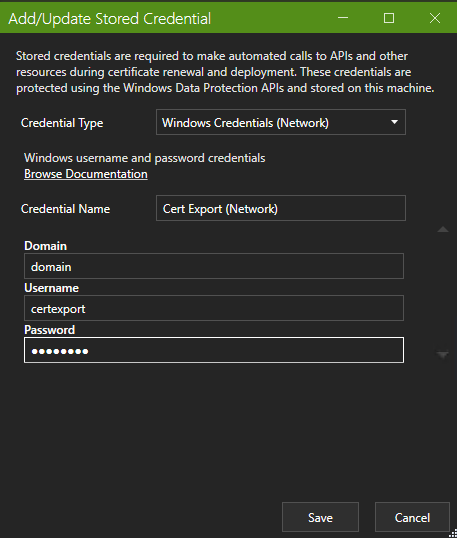
The created cert should be exported to a windows network share and I’m using the “Export Certificate” Task with Windows network credentials (as before).
This has worked before but now it’s always showing an error which states that the password is wrong.
022-09-19 20:01:02.061 +02:00 [ERR] Export failed with error: System.Security.Cryptography.CryptographicException: Das angegebene Netzwerkkennwort ist falsch.
bei System.Security.Cryptography.CryptographicException.ThrowCryptographicException(Int32 hr)
bei System.Security.Cryptography.X509Certificates.X509Utils._LoadCertFromBlob(Byte[] rawData, IntPtr password, UInt32 dwFlags, Boolean persistKeySet, SafeCertContextHandle& pCertCtx)
bei System.Security.Cryptography.X509Certificates.X509Utils.LoadCertFromBlob(Byte[] rawData, IntPtr password, UInt32 dwFlags, Boolean persistKeySet, SafeCertContextHandle pCertCtx)
bei System.Security.Cryptography.X509Certificates.X509Certificate.LoadCertificateFromBlob(Byte[] rawData, Object password, X509KeyStorageFlags keyStorageFlags)
bei System.Security.Cryptography.X509Certificates.X509Certificate2..ctor(Byte[] rawData, String password)
bei Certify.Providers.DeploymentTasks.CertificateExport.GetCertComponentsAsPEMString(Byte[] pfxData, String pwd, ExportFlags flags)
bei Certify.Providers.DeploymentTasks.CertificateExport.<Execute>d__8.MoveNext()
I’ve tested the credentials multiple times and they work.
Any ideas?
/nightmare1942
Despite the .net error message this is probably unrelated to your network credentials as the process being run here (nd the exception being shown) is when it tries to extract the certificate components from the PFX file.
Perhaps you have recently set or removed a password on your PFX (Certficate > Advanced > Signing & Security) and if you have done so but not requested a new version of the certificate then the file you currently have will not have the most recent password.
You are right it wasn’t related to these credentials.
I did not remove or change anything for the PFX/P12 password but I recognized that when trying to use a different user than “Local System” for the windows service there will be no password set for the PFX even though it’s configured.
This lead to an exception later at the deployment process/task.
After changing it back it’s working again.
Can you explain why the P12 password is not set when using a different service user?
The PFX password would theoretically be the same but the app will fail the decrypt the password you have stored if you change the service account user. I really don’t recommend changing the service account user because:
- stored credentials and account details can only be decrypted by the account which created them
- the service generally needs to write to the machine certificate store and IIS config, both of which require admin rights.
- we do not currently test the app against alternative user accounts.
About changing the service account user:
I normally let every 3rd party service run as a specific user with limited rights. This will harden the server a little more if it’s not an admin account with all rights and it is not neccessary to be admin to be able to write to the local cert store. But it needs to have certain rights to do so, that’s true. And setting these to a specific user can be cumbersome.
And for the encryption part: You are totally write and it’s good that it is that way.
I still think it would be nice to have an error message displaying when it tries to set the password for the PFX store if it cannot decrypt it. At least IMHO it should be somehow made visible unto the user that there is no password set.
1 Like